GCP
One of the tools an IT auditor can leverage to perform monitoring in GCP is Google Cloud Monitoring.
Google Cloud Monitoring
Google Cloud Monitoring collects metrics of Google Cloud resources. IT auditors can leverage Google Cloud Monitoring to gain real-time visibility into GCP, as seen in Figure 10.35. To launch the Monitoring explorer, take the following steps:
- Navigate to GCP.
- Select Monitoring | Dashboards.
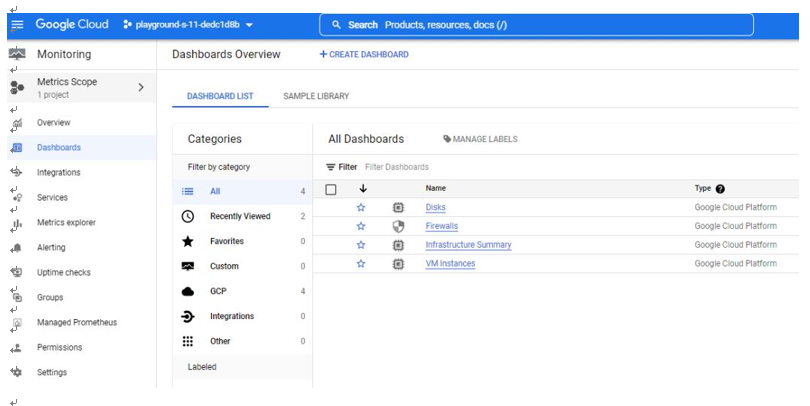
Figure 10.35 – Google Cloud Monitoring
The Dashboards feature within Google Cloud Monitoring provides dashboards of various resources, such as Disks, Firewalls, Infrastructure Summary, and VM instances. As an example of an assessment, let us review the FIREWALLS dashboard, as seen in Figure 10.36:
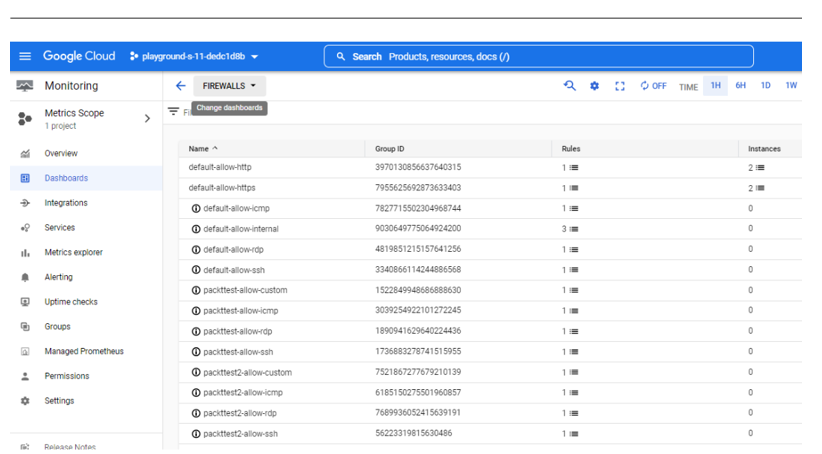
Figure 10.36 – Google Cloud Monitoring | Dashboards
If we dig deeper, we can note that there is an ingress/inbound rule that allows traffic from any IP address on the internet (0.0.0.0/0) to port TCP 22 (SSH), as seen in Figure 10.37:
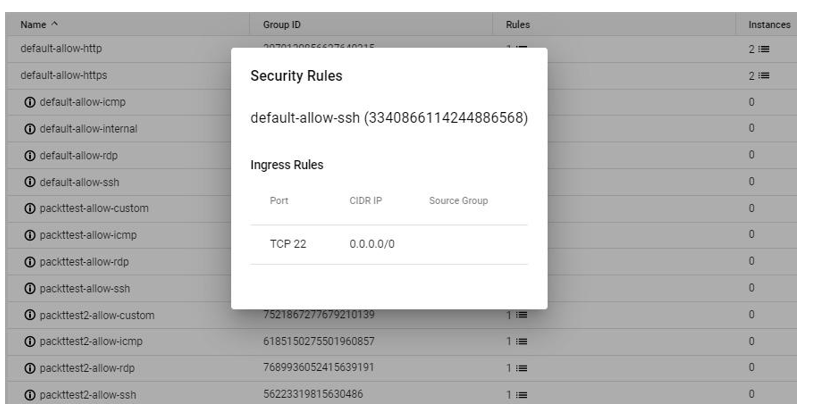
Figure 10.37 – Security Rules
This particular rule should pique an IT auditor’s interest as port 22 is a network protocol that has system administrator capability. Attackers can use various brute force techniques to gain access to GCP resources using remote server administration ports, such as 22; therefore the IT auditor should inquire about the business need to have port 22 open to anyone on the internet.
Another useful feature of Google Cloud Monitoring is Alerting. The Alerting feature allows you to trigger an alert based on a predefined metric, as seen in Figure 10.38. An IT auditor can create an alerting policy so that they are notified when the performance of a resource doesn’t meet the criteria defined. To launch the Cloud Monitoring explorer, take the following steps:
- Navigate to the Google Cloud portal.
- Select Monitoring | Alerting.
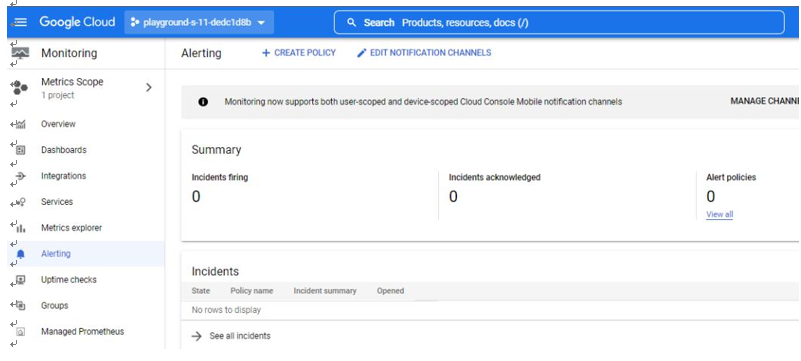
Figure 10.38 – Google Cloud Monitoring | Alerting
As an example, we can add a metric, such as Audited Resource, as seen in Figure 10.39:
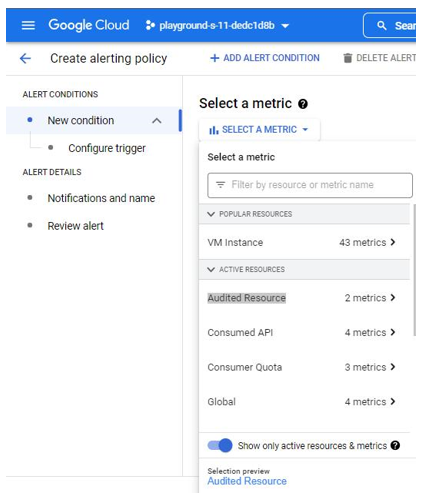
Figure 10.39 – Create alerting policy | Audited Resource metric
We’ve now completed our walk-through of monitoring and alerting policies within AWS, Azure, and GCP. IT auditors should now have a repertoire of toolsets they can use to effectively perform their audits in the cloud.
Summary
In this chapter, we performed a walk-through of change management, logging, and monitoring policies for the AWS, Azure, and GCP platforms. We specifically covered how to assess change management controls, audit and logging configurations, and change management and configuration policies. Finally, we reviewed how an IT auditor can leverage monitoring and alerting policies.
We have reached the end of the book. Well done! I want to thank you for sharing this journey with us. The book has provided a roadmap for how to build and execute effective cloud auditing plans for AWS, Azure, and GCP. We hope this will be a valuable resource that you can utilize, and that it enables you to secure and add real value to the organizations that you audit.